GNU/Linux CentOS 7 Installing Social Engineering Toolkit – QuickStart Guide
Hi! The Tutorial shows you Step-by-Step How to Install Social Engineering Toolkit in CentOS 7.x GNU/Linux Desktop.
And Social Engineering Toolkit in CentOS 7 is an TrustedSec Open-Source Python-driven Tool aimed at penetration testing around Social-Engineering.
With over two million Downloads, it is the standard for Social-Engineering Penetration Tests and supported heavily within the security community.
Here are some Key Points of SEToolkit:
- Purpose: The primary purpose of the Social Engineering Toolkit is to automate and streamline social engineering attacks, which aim to manipulate individuals into divulging confidential information, performing actions, or compromising security measures.
- Features: SET provides a wide range of features for conducting social engineering attacks, including creating phishing websites, generating malicious payloads, conducting spear-phishing campaigns, creating fake access points, and more.
- Phishing Attacks: One of the most common uses of SET is to create phishing websites that mimic legitimate websites (such as login pages for social media or email services). These phishing websites are designed to trick users into entering their credentials, which are then captured by the attacker.
- Payload Generation: SET can generate various types of malicious payloads, including backdoors, keyloggers, and Metasploit payloads. These payloads can be used to exploit vulnerabilities in target systems and gain unauthorized access.
- Spear-Phishing Campaigns: SET allows users to conduct targeted spear-phishing campaigns, where customized phishing emails are sent to specific individuals or groups. These emails are often crafted to appear legitimate and exploit the trust of the recipients.
- Integration with Metasploit: SET integrates with the Metasploit Framework, a widely used penetration testing tool, to automate the exploitation of vulnerabilities discovered during social engineering attacks.
- Educational Purposes: While SET can be used for malicious purposes, it is also commonly used for educational and training purposes, allowing security professionals to understand and defend against social engineering attacks.
- Legal Considerations: It’s important to note that conducting social engineering attacks without proper authorization is illegal and unethical. The Social Engineering Toolkit should only be used in controlled environments and with explicit permission from the target organization for legitimate security testing purposes.
Especially relevant: TrustedSec believes that Social-Engineering is one of the hardest Attacks to protect against and now one of the most prevalent.
Finally, this guide includes detailed instructions about to Getting-Started with Social Engineering Toolkit on CentOS.
1. Launching Shell Emulator
Open a Terminal window
(Press “Enter” to Execute Commands)In case first see: Terminal QuickStart Guide.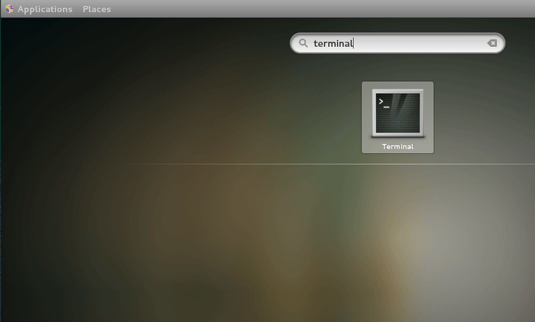
Contents